Data generated in the medical domain – no matter if patient records or other highly sensitive information (e.g., genome sequence data) – is among the most sensitive data and worth protecting with cutting edge technology: QKD and fragmentiX Secret Sharing.
In this use case a QKD protected Secret Sharing network is established to connect the high containment laboratory at Medical University of Graz (producing the sensitive data) and a data center in Vienna. This will enable collaborative biomedical research and provide a high security data repository as innovative solution to comply with international requirements for research that has to be protected because dual use research of concern (DURC) issues.
Further, the scalability of the solution will be demonstrated by connecting other Austrian key actors in pathogen research as well as governmental organizations, resulting in an extended protected connection to St. Johann, as established in the Governmental use case.
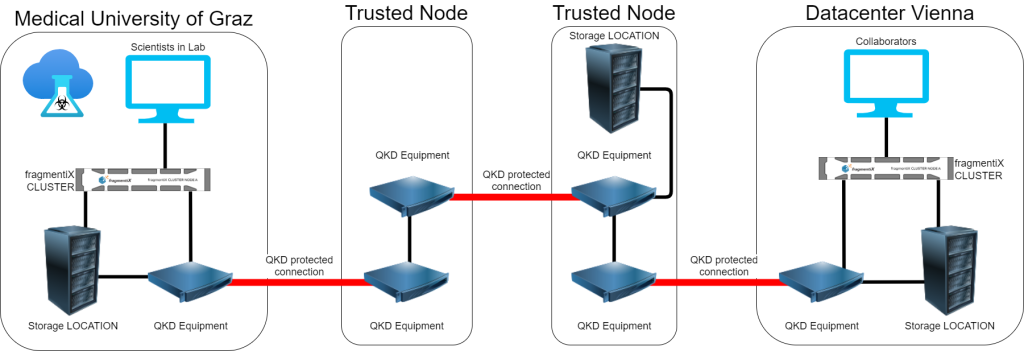
To establish a secure connection over the long distance between Graz and Vienna, prototypes of two trusted repeater nodes which are developed in QCI-CAT are deployed along the way. The architecture and design is shown in the graphic:
Medical University Graz: Scientists producing Data, fragmentiX CLUSTER, Storage LOCATION and QKD equipment
Trusted node 1: QKD equipment for two links
Trusted node 2: QKD equipment for two links and a Storage LOCATION
Data center Vienna: fragmentiX CLUSTER, Storage LOCATION and QKD equipment and possible Collaborators
In coordination with the Medical University of Graz, the hardware installation of the QKD equipment will be carried out by technicians of AIT and the setup and integration of the fragmentiX Secret Sharing Appliance will be performed by fragmentiX. The same procedure will be applied to the data center in Vienna.
After the completion of the two trusted node prototypes, they will be deployed by qualified fragmentiX personell. The QKD devices will be configured by fragmentiX together with AIT technicians. Once all network infrastructure (including QKD devices) is set up, configured and tested, the secret sharing network will be established. After a testing period, the secret sharing will be integrated in the scientists’ workflow.
The use case will be closed by an evaluation of the workflow and user experience.
ABOUT QCI-CAT
Building on the long research experience of Austrian institutions in the field of quantum technologies, the project QCI-CAT aims at an adoption of modern encryption technology based on QKD for highly secure communication between public authorities.
QCI-CAT will investigate and verify new security applications for public authorities, such as secret sharing and message authentication.
Additionally, QCI-CAT will also leverage a research testbed for new technological approaches such as the combination of post-quantum encryption with QKD, long-distance QKD with secured trusted nodes and field trials of quantum repeaters.